B O N A V E N T U R E
15
W
I
N
T
E
R
2
0
1
5
-
1
6
Never use your debit card online.
Levels of protection for credit
card fraud are typically
greater than those for debit
cards. Watch out for email
links. Scammers will send out very
legitimate looking emails with links in
them. Click on the link and you've
opened your computer up to the bad
guys.
Dr. Michael Hoffman
Associate Provost, Chief Information
Officer at St. Bonaventure University
You are a security layer.
Many kinds
of threat rely on social engineer-
ing, psychologically manipu-
lating a victim into doing
something that will enable
the attacker to achieve his
aims. If you can maintain a reason-
able level of skepticism and remem-
ber that successful social
engineering may use the carrot or
the stick (or both), you can save
yourself a lot of grief. Don't fall into
the trap of thinking that security
software or your favorite operating
system will save you.
David Harley
Senior Research Fellow at ESET North
America
Set your smartphone to lock after
a short idle time,
and set it to
require authentication for un-
locking. If at all possible, use
something stronger than a
simple-minded four-digit PIN.
Neil Rubenking
Lead Analyst at PC Magazine
Mobile devices are an open gate to
our privacy, secrets, and
money
(mobile banking). Be
very careful what apps you
choose to install and pay spe-
cial attention to what permis-
sions each app is requesting. For
instance, it doesn't quite make sense
for a weather app to demand access
to your photos, does it?
Andrei Petrus
Product Manager at Avira
gether with Drs. Harry Sedinger and Dalton
Hunkins, Andrianoff cobbled together a cur-
riculum and the first students with a com-
puter science degree graduated in 1983. The
program broke off from mathematics in
1989 to become its own department.
He first heard of email in 1985 when profes-
sors at colleges across the state, including St.
Bonaventure, began communicating electroni-
cally via NYSERNet, a consortium of visionary
public and private New York state institutions
to provide high-speed network connectivity to
advance research and educational initiatives.
Thirty years later, advances in cybersecurity
haven't kept pace with the explosion of the In-
ternet and the desire to digitize every morsel
of our lives.
"The problem is that too many of us still
treat the digital world in the same way we
treat the physical world," Andrianoff said.
"We think, `If you're the only person I'm com-
municating with, you're the only person who
hears me.' But when you communicate digi-
tally, anyone who's out there who wants to
get that information can get it."
That's why, he said, cybersecurity might be
"as much a social problem" as a technical
one: "People don't yet fully comprehend the
nature of their interactions in the digital
world."
Levine sees the tendency even in people
who presumably should know better.
"I started a game with prospective stu-
dents," said Levine. "If a student comes and
talks with me about cybersecurity, at some
point I'll just stop and ask them, `What's your
email password?'
"Fortunately, none of them have told me,
but a couple have come close," he said.
"Then I look at them and say: `If you, who
are with it, who are here to talk with me
about cybersecurity, considered even for an
instant answering that question, what do
you expect somebody who's not security-
aware to do?'"
THE NOTION THAT THE DIGITAL
world
can ever be 100 percent secure for an indi-
vidual is 99.9 percent false, Levine said.
"If you want to guarantee that nobody
ever gets your password, there's a very sim-
ple way: Have no accounts anywhere,"
Levine said. "In this day and age, you just
can't do that anymore. You'd have to be an
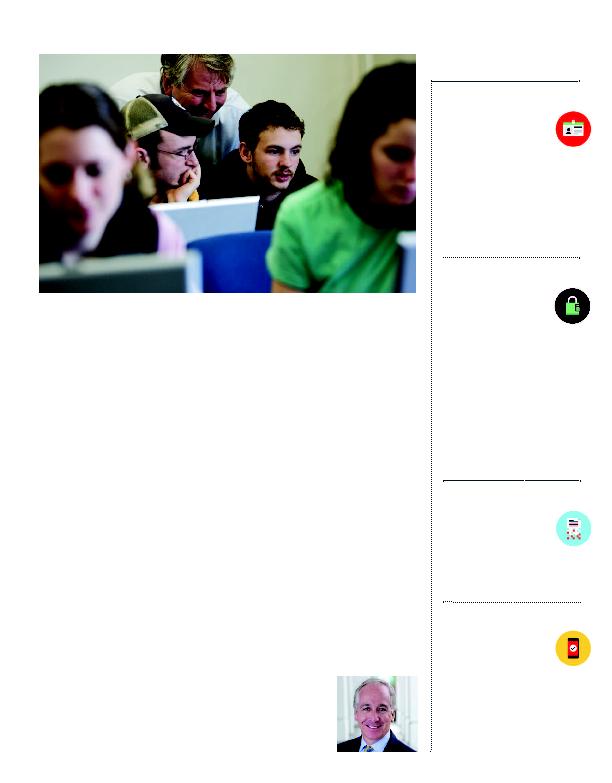
Computer science professor Dr. David Levine (center) says the goal of SBU's cybersecurity pro-
gram is that "our dream is that our graduates will be able to speak to both sides -- the tech-
nical and the managerial."
Cyber
Tips
I don't think I've seen a risk management
issue like cybersecurity in my
35 years in the workplace.
"
''
Paul McDonald, '80, senior executive director of Robert Half